users of smart cards are required to enter a quizlet A smart card is a card with an embedded chip or microprocessor. This embedded technology allows a smart card to store vast amounts of data and to perform calculations. For example, a . 8. Check Price on Amazon. 1. ROSEEKA 20Pcs Rewritable NFC Tags – Ntag .7740 Smart Card, Fingerprint reader, & NFC. . 7740 Smart Card, FIPS Fingerprint reader, & .
0 · flashcards for electronic banking
1 · debit card quizlet
2 · cash card quizlet
Botw 23/24/25/26 Cards in 1 Nfc Game Cards Pack for the Legend of Zelda Breath of the Wild With Mini Crystal Case (NS Game Card Size) from $3.99 $8.99. 26 Cards in 1 Pack 25 Cards in 1 Pack 24 Cards in 1 Pack 23 Cards in .
Smart cards are typically used to provide secure, multi-factor authentication. Only users with the smart card and who know the associated PIN number are allowed to authenticate. Computers that require a smart card must have a smart card reader attached.
A smart card is a card with an embedded chip or microprocessor. This embedded technology allows a smart card to store vast amounts of data and to perform calculations. For example, a .Users of smart cards are required to enter a _____ to be authenticated. personal identification number A ________ has a microchip that is loaded with identifying data.Answer to Users of smart cards are required to enter a _____Study eight different ways with Quizlet! Study modes, activities, AI-powered study tools, and step-by-step question and textbook solutions make reviewing any subject engaging and effective. .
Users of smart cards are required to enter a _____ to be authenticated. A) Social Security number B) public key C) personal identification number D) private key Users of smart cards are typically required to enter a C) personal identification number, or PIN, to be authenticated. A PIN is a secure code that the user must enter correctly .
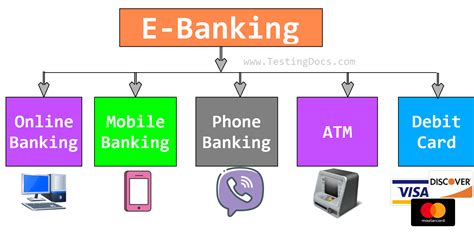
flashcards for electronic banking
Users of smart cards are required to enter a ________ to be authenticated. 1.Personal identification number, 2.Trojan horses, 3.Data (base) administration, 4.Provide physical security.When users log in to the network locally, they must provide their username and password. When users log in to the network remotely, they must provide their username, password, and smart . Sarah has deployed a private cloud infrastructure that requires users to insert a smart card into their computer or into a card reader in order to authenticate them to use the .
Smart cards are typically used to provide secure, multi-factor authentication. Only users with the smart card and who know the associated PIN number are allowed to authenticate. Computers that require a smart card must have a smart card reader attached.A smart card is a card with an embedded chip or microprocessor. This embedded technology allows a smart card to store vast amounts of data and to perform calculations. For example, a smart card could contain a user's PIN and the monetary value remaining on the card.Users of smart cards are required to enter a _____ to be authenticated. personal identification number A ________ has a microchip that is loaded with identifying data.Answer to Users of smart cards are required to enter a _____
Study eight different ways with Quizlet! Study modes, activities, AI-powered study tools, and step-by-step question and textbook solutions make reviewing any subject engaging and effective. Here's a quick look at all the ways you can study with Quizlet.
Users of smart cards are required to enter a _____ to be authenticated. A) Social Security number B) public key C) personal identification number D) private key Users of smart cards are typically required to enter a C) personal identification number, or PIN, to be authenticated. A PIN is a secure code that the user must enter correctly to gain access to the information or capabilities of the smart card.Users of smart cards are required to enter a ________ to be authenticated. 1.Personal identification number, 2.Trojan horses, 3.Data (base) administration, 4.Provide physical security.When users log in to the network locally, they must provide their username and password. When users log in to the network remotely, they must provide their username, password, and smart card. Which two statements are true regarding your organization's security?
Sarah has deployed a private cloud infrastructure that requires users to insert a smart card into their computer or into a card reader in order to authenticate them to use the applications. The smart card is associated with a certificate for each user, which is verified against a certificate authority.Smart cards are typically used to provide secure, multi-factor authentication. Only users with the smart card and who know the associated PIN number are allowed to authenticate. Computers that require a smart card must have a smart card reader attached.
A smart card is a card with an embedded chip or microprocessor. This embedded technology allows a smart card to store vast amounts of data and to perform calculations. For example, a smart card could contain a user's PIN and the monetary value remaining on the card.Users of smart cards are required to enter a _____ to be authenticated. personal identification number A ________ has a microchip that is loaded with identifying data.Answer to Users of smart cards are required to enter a _____Study eight different ways with Quizlet! Study modes, activities, AI-powered study tools, and step-by-step question and textbook solutions make reviewing any subject engaging and effective. Here's a quick look at all the ways you can study with Quizlet.
Users of smart cards are required to enter a _____ to be authenticated. A) Social Security number B) public key C) personal identification number D) private key
Users of smart cards are typically required to enter a C) personal identification number, or PIN, to be authenticated. A PIN is a secure code that the user must enter correctly to gain access to the information or capabilities of the smart card.Users of smart cards are required to enter a ________ to be authenticated. 1.Personal identification number, 2.Trojan horses, 3.Data (base) administration, 4.Provide physical security.
When users log in to the network locally, they must provide their username and password. When users log in to the network remotely, they must provide their username, password, and smart card. Which two statements are true regarding your organization's security?
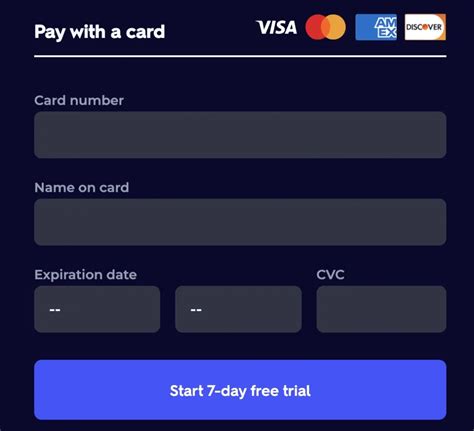
debit card quizlet
$14.33
users of smart cards are required to enter a quizlet|flashcards for electronic banking