rfid e-field protection RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by . Just dip or tap to pay. Be ready for every sale with Square Reader for contactless and chip. .Our powerful and intuitive app allows you to effortlessly read, write, manage, and secure NFC card data, including the added convenience of .
0 · rfid scanner protection
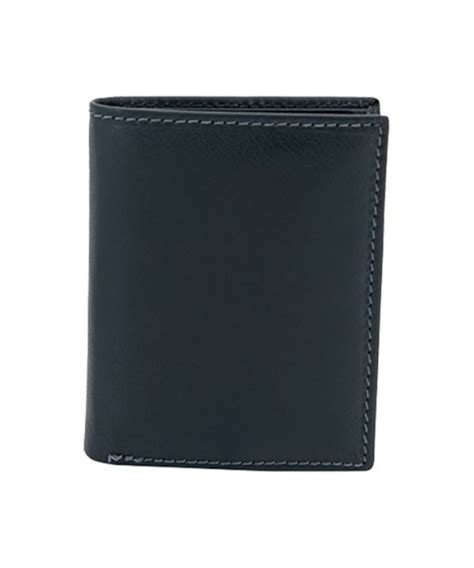
1 · rfid guidelines
2 · rfid blocking products
3 · rfid blocking devices
4 · retail rfid identification
5 · how to protect against rfid
6 · are rfid blocking products necessary
7 · advanced rfid protection
NFC Tag in your Rolex. (in your warranty card) So, I laid my phone on top of my watch box this .
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .
OECD Basic Principles: Guidelines on the Protection of Privacy and Transborder Flows of Personal Data..................................6-4RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .
OECD Basic Principles: Guidelines on the Protection of Privacy and Transborder Flows of Personal Data..................................6-4Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder called a .
We investigated RFID-related crime and spoke to an expert to find out. From smart wallets to smart clothing, RFID-blocking products are big business, but are you really at risk .Protect cards from electronic pickpocketing with patented VAULTCARD's superior jamming technology, offering unmatched security against RFID theft.It provides information about protection for people against health effects from direct, non- medical exposures to both short- and long-term, continuous and discontinuous RF electromagnetic . Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers .
Key criteria defined in these documents are frequencies of interest, RF Fields (i.e., Magnetic (or H-Field), Electric (or E-Field), Plane Wave (PW), and Microwave (MW), the SEdB, and the test .
Our solution is based on an RFID chip shielding with an opaque metal. The Faraday type of the enclosure has a small aperture, which suppresses electromagnetic field leakage from the .Here we introduce a new concept of anapole-enabled security, prohibiting far-field attacks by utilizing fundamental laws of physics. Our design is based on radiationless electromagnetic .RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by .
OECD Basic Principles: Guidelines on the Protection of Privacy and Transborder Flows of Personal Data..................................6-4
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder called a . We investigated RFID-related crime and spoke to an expert to find out. From smart wallets to smart clothing, RFID-blocking products are big business, but are you really at risk .Protect cards from electronic pickpocketing with patented VAULTCARD's superior jamming technology, offering unmatched security against RFID theft.It provides information about protection for people against health effects from direct, non- medical exposures to both short- and long-term, continuous and discontinuous RF electromagnetic .
Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers .Key criteria defined in these documents are frequencies of interest, RF Fields (i.e., Magnetic (or H-Field), Electric (or E-Field), Plane Wave (PW), and Microwave (MW), the SEdB, and the test .Our solution is based on an RFID chip shielding with an opaque metal. The Faraday type of the enclosure has a small aperture, which suppresses electromagnetic field leakage from the .
smart card manafactuers
rfid scanner protection

If you have an android phone, the cards/stickers is the cheapest route. If not, and you don't .
rfid e-field protection|rfid guidelines