nfc credit card stealer You can a credit card with any NFC-equipped phone, but the CV2 code will change with each read, and reusing a code or using codes in the wrong order automatically voids the card number. Shop on eBay. Opens in a new window or tab. Brand New. $20.00. or Best Offer . from United .
0 · cuamckuu/nfc
1 · Android malware steals payment card data using
This was done during an Android Mod in SUTD, where we created a time-tracking app called SnapTrack. Scouring the internet and finding useful material for my use-case was hard. I .
cuamckuu/nfc
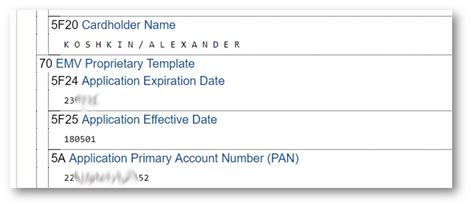
Newly discovered Android malware steals payment card data using an infected device’s NFC reader and relays it to attackers, a novel technique that effectively clones the card so it can be used at.
Newly discovered Android malware steals payment card data using an infected device’s NFC reader and relays it to attackers, a novel technique that effectively clones the card so it can be used at.Kick-ass contactless credit card reader. With nfc-frog you can extract data from many contactless EMV credit cards. Also it supports mulitiple reading modes, so you can choose mode which suits you best. Tested with: Visa, MasterCard, MIR (other cards should work too). A new Android malware named NGate can steal money from payment cards by relaying to an attacker's device the data read by the near-field communication (NFC) chip.
smart card vs magnetic stripe
Android malware steals payment card data using
You can a credit card with any NFC-equipped phone, but the CV2 code will change with each read, and reusing a code or using codes in the wrong order automatically voids the card number.
Cybercriminals have reportedly found a way to steal from smartphone users by exfiltrating the data read by their device's near-field communications (NFC) chip. As reported by The Hacker News, the malware in question has been dubbed NGate by security researchers at ESET, and it steals NFC data to clone contactless credit and debit cards on a hacker’s.The Hunter Cat NFC is the latest security tool for contactless (Near Field Communication) used in access control, identification and bank cards. Specially created to identify NFC readers and sniffing tools, with this tool you can audit, read or emulate cards of different types.NGate malware is the latest insidious threat lurking in the [android] devices. Cleverly designed, it exploits NFC (Near Field Communication) technology to steal credit card data.
ESET Research uncovers Android malware that relays NFC data from victims’ payment cards, via victims’ mobile phones, to the device of a perpetrator waiting at an ATM.
The cyberattack, based on both a complex social engineering scheme and the use of a new Android malware, is capable of stealing users’ near field communication data to withdraw cash from. Newly discovered Android malware steals payment card data using an infected device’s NFC reader and relays it to attackers, a novel technique that effectively clones the card so it can be used at.Kick-ass contactless credit card reader. With nfc-frog you can extract data from many contactless EMV credit cards. Also it supports mulitiple reading modes, so you can choose mode which suits you best. Tested with: Visa, MasterCard, MIR (other cards should work too).
A new Android malware named NGate can steal money from payment cards by relaying to an attacker's device the data read by the near-field communication (NFC) chip. You can a credit card with any NFC-equipped phone, but the CV2 code will change with each read, and reusing a code or using codes in the wrong order automatically voids the card number. Cybercriminals have reportedly found a way to steal from smartphone users by exfiltrating the data read by their device's near-field communications (NFC) chip.
smart card scanner app
As reported by The Hacker News, the malware in question has been dubbed NGate by security researchers at ESET, and it steals NFC data to clone contactless credit and debit cards on a hacker’s.
The Hunter Cat NFC is the latest security tool for contactless (Near Field Communication) used in access control, identification and bank cards. Specially created to identify NFC readers and sniffing tools, with this tool you can audit, read or emulate cards of different types.
NGate malware is the latest insidious threat lurking in the [android] devices. Cleverly designed, it exploits NFC (Near Field Communication) technology to steal credit card data.
ESET Research uncovers Android malware that relays NFC data from victims’ payment cards, via victims’ mobile phones, to the device of a perpetrator waiting at an ATM.

$299.99
nfc credit card stealer|cuamckuu/nfc