testing tag cmc rfid blocking Typically, companies design a new tag antenna and then place the tag within an anechoic . Yes they are perfectly fine. If you’re considering this I would suggest buying .
0 · testing rfid blocking
1 · test rfid blocking credit card
2 · test rfid blocking card holder
3 · how to check rfid signals
4 · how to check rfid blockage
Shop COMC's extensive selection of 1993-2024 steven jackson st. louis rams football cards. .
Blocker tag attack is one of the denial-of-service (DoS) attacks that threatens the privacy and .

CMCID,a product department of CMC,Commitment to Internet product development, design, . In response to tag conflicts in radio frequency identification (RFID) systems, a .Typically, companies design a new tag antenna and then place the tag within an anechoic . An industry has sprung up to make wallets and accessories that block hackers .
Discover how these RFID blocking cards provide protection against .Blocker tag attack is one of the denial-of-service (DoS) attacks that threatens the privacy and security of RFID systems. The attacker interferes with the blocked tag by simulating a fake tag with the same ID, thus causing a collision of message replies.
The easiest way to test the RFID blocking of your wallet, card holder or other device is to head to a pay point that lets you scan your card instead of swiping. You’re looking for a PayPass terminal in the US. Simply scan your wallet with your card in, perhaps asking for permission to try it first.CMCID,a product department of CMC,Commitment to Internet product development, design, production and manufacturing, products include RFID readers, RFID tags, RFID middleware, industrial data acquisition, embedded computer terminals. We invite system integration vendors, partners are welcome to our company site visits.
In response to tag conflicts in radio frequency identification (RFID) systems, a novel hybrid blocking query tree algorithm is suggested that leverages blocking prediction and child node.
Typically, companies design a new tag antenna and then place the tag within an anechoic chamber, which is intended to block out electromagnetic energy from exterior sources and absorb energy within the chamber, in order to prevent reflected energy from reaching the tag. An industry has sprung up to make wallets and accessories that block hackers from "skimming" data wirelessly through radio frequency identification. But some experts say there's little need to . Discover how these RFID blocking cards provide protection against unauthorized scanning of your credit cards and personal information.
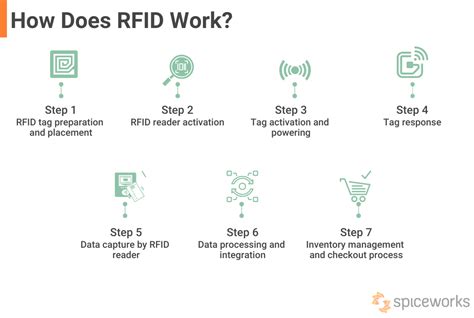
What Is RFID Blocking? “RFID blocking is when something is used to reduce the transmitted signal of the RFID chip to virtually make it impossible for a reader to catch the signal,” says Schlossberg. “It virtually eliminates the ability for the chip to . The process involves three main steps: tag programming, tag detection, and information retrieval. 1. Tag Programming: Each RFID tag contains a unique identifier, known as an Electronic Product Code (EPC), which is programmed during manufacturing. To effectively avoid the tag collision problem and improve the reading performance of RFID systems, two advanced tag identification algorithms namely Adaptive M-ary tree slotted Aloha (AMTS) based on the characteristics of Aloha .Blocker tag attack is one of the denial-of-service (DoS) attacks that threatens the privacy and security of RFID systems. The attacker interferes with the blocked tag by simulating a fake tag with the same ID, thus causing a collision of message replies.
The easiest way to test the RFID blocking of your wallet, card holder or other device is to head to a pay point that lets you scan your card instead of swiping. You’re looking for a PayPass terminal in the US. Simply scan your wallet with your card in, perhaps asking for permission to try it first.CMCID,a product department of CMC,Commitment to Internet product development, design, production and manufacturing, products include RFID readers, RFID tags, RFID middleware, industrial data acquisition, embedded computer terminals. We invite system integration vendors, partners are welcome to our company site visits. In response to tag conflicts in radio frequency identification (RFID) systems, a novel hybrid blocking query tree algorithm is suggested that leverages blocking prediction and child node.Typically, companies design a new tag antenna and then place the tag within an anechoic chamber, which is intended to block out electromagnetic energy from exterior sources and absorb energy within the chamber, in order to prevent reflected energy from reaching the tag.
An industry has sprung up to make wallets and accessories that block hackers from "skimming" data wirelessly through radio frequency identification. But some experts say there's little need to . Discover how these RFID blocking cards provide protection against unauthorized scanning of your credit cards and personal information.
What Is RFID Blocking? “RFID blocking is when something is used to reduce the transmitted signal of the RFID chip to virtually make it impossible for a reader to catch the signal,” says Schlossberg. “It virtually eliminates the ability for the chip to . The process involves three main steps: tag programming, tag detection, and information retrieval. 1. Tag Programming: Each RFID tag contains a unique identifier, known as an Electronic Product Code (EPC), which is programmed during manufacturing.

testing rfid blocking

rfid race timing systems australia
In this section, we’ll explore how, much to everyone’s chagrin, there is no “silver bullet” here to solve the issue of NFC interference. There . See more
testing tag cmc rfid blocking|testing rfid blocking