rfid tag 2 factor authentication Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and . It is an electronic format of a business card that can be easily shared with others through email, text, social media, NFC technology or QR codes. A digital business card typically includes the same information as a paper card, such .
0 · what is rfid verification
1 · rfid verification process
2 · rfid authentication tool
3 · rfid authentication
4 · hid rfid authentication
5 · hid rfid
6 · electronic id rfid
7 · authx rfid
The 2015 NFL Playoff Schedule kicked off on Saturday, Jan. 9, 2016 with two Wild-Card games. In Super Bowl 50, the Denver Broncos defeated the Carolina Panthers 24-10 at Levi’s Stadium in Santa .
Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and .

hp uefi bios settings for smart card reader
RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable .Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and logout authentication, saving time without sacrificing security.RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable device, numerous use cases become possible.
what is rfid verification
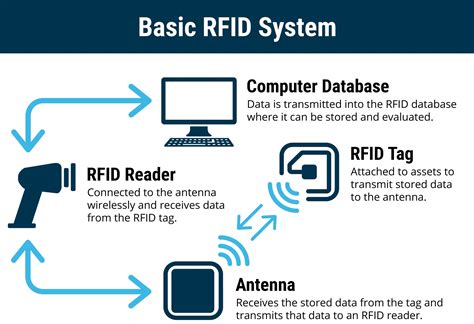
Radio frequency identification (RFID) enables you to read data encoded in RFID chips using specialized equipment—RFID readers. Unlike RFID, near-field communication, or NFC, is a two-way channel for transferring data between devices like phones and smartwatches.Key fobs and multifactor authentication. Key fobs are also used as one of the authentication factors for devices that require two-factor (2FA) or multifactor authentication (MFA). These authentication methods help safeguard a company's network, devices, applications and data.
Protect your workforce identities, networks and data with passwordless, phishing-resistant and traditional multi-factor authentication. Talk to an MFA expert. You can set up the optional 2-factor RFID authentication available on the DL1000V32F and the DL500V32F by following the below instructions : **RFID is available ONLY on DL3FE models provisioned with an RFID chip as of January 1st, 2017**. The DL3/FE device can be paired with up to five RFID tags.This page describes how to configure an RFID badge using Evidians' solution. Authentication Manager is compliant with newest RFID readers. You can authenticate using latest Cherry or NFC readers, among other devices (Hitachi for example).You can set up the optional 2 factor RFID authentication available on the DL1000V32F and the DL500V32F by following the below instructions :
rfid verification process
rfid authentication tool
The development of a two-factor RFI and biometric fingerprint authentication-based security scheme is described in this work. It can offer effective control facilities to prevent entry.
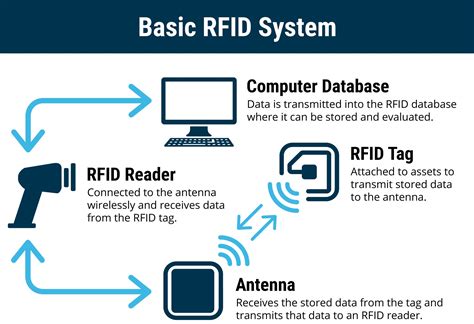
The full authentication process looks like this: The user scans their RFID tag using the RFID & NFC expansion (If you’re unfamiliar with NFC communication, fear not as all is explained in the tutorial). The Omega will send the unique serial number of the scanned tag to a server for verification.
Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and logout authentication, saving time without sacrificing security.
RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable device, numerous use cases become possible. Radio frequency identification (RFID) enables you to read data encoded in RFID chips using specialized equipment—RFID readers. Unlike RFID, near-field communication, or NFC, is a two-way channel for transferring data between devices like phones and smartwatches.Key fobs and multifactor authentication. Key fobs are also used as one of the authentication factors for devices that require two-factor (2FA) or multifactor authentication (MFA). These authentication methods help safeguard a company's network, devices, applications and data.Protect your workforce identities, networks and data with passwordless, phishing-resistant and traditional multi-factor authentication. Talk to an MFA expert.
You can set up the optional 2-factor RFID authentication available on the DL1000V32F and the DL500V32F by following the below instructions : **RFID is available ONLY on DL3FE models provisioned with an RFID chip as of January 1st, 2017**. The DL3/FE device can be paired with up to five RFID tags.This page describes how to configure an RFID badge using Evidians' solution. Authentication Manager is compliant with newest RFID readers. You can authenticate using latest Cherry or NFC readers, among other devices (Hitachi for example).
You can set up the optional 2 factor RFID authentication available on the DL1000V32F and the DL500V32F by following the below instructions : The development of a two-factor RFI and biometric fingerprint authentication-based security scheme is described in this work. It can offer effective control facilities to prevent entry.
rfid authentication
hid rfid authentication
Find out which teams are winning the 2024 playoff race. Check out the NFL Playoff Picture for the latest team performance stats and playoff eliminations. Learn more.
rfid tag 2 factor authentication|rfid authentication