authorization of readers in rfid with password and keys Learn how HID Global offers RFID technology for secure, efficient and convenient identity verification across various access scenarios. Explore solutions, products, use cases, benefits and resources for RFID authentication. 5. Minnesota Vikings (7-2) Minnesota is the No. 5 seed in the NFC, trailing Detroit by a game for the division lead. The Vikings are the top wild-card team in the conference.
0 · rfid authentication tool
1 · rfid authentication protocol
2 · rfid authentication algorithm
3 · rfid authentication
4 · hid rfid support
5 · hid rfid authentication
6 · hid rfid
There are 4 Amazon credit cards (more if you count the Prime and non-Prime versions as separate cards) - a Visa personal card through Chase, a personal store card (can only be used on Amazon) through Synchrony, a secured store card through Synchrony, and a business card .Customers load their American Express® Card information onto an NFC-enabled phone: NFC .
Learn how HID Global offers RFID technology for secure, efficient and convenient identity verification across various access scenarios. Explore solutions, products, use cases, benefits and resources for RFID authentication.Compared to traditional key or password systems, RFID systems enable fast contactless identification, allowing users to simply bring the RFID card close to the reader. The system can .Learn how HID Global offers RFID technology for secure, efficient and convenient identity verification across various access scenarios. Explore solutions, products, use cases, benefits and resources for RFID authentication.
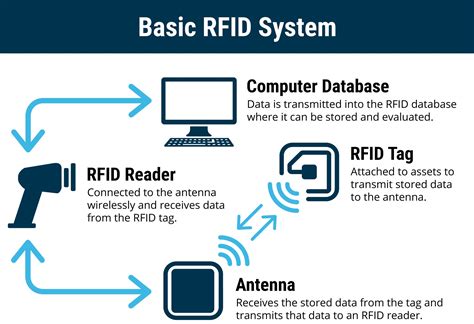
Compared to traditional key or password systems, RFID systems enable fast contactless identification, allowing users to simply bring the RFID card close to the reader. The system can also generate real-time entry and exit records for easy management and auditing. RFID reader: This device reads the information stored on the RFID tags and sends it to the access control system to allow authorization. When someone presents their RFID card, ID badge, or key fob to an RFID-enabled door, the reader initiates a signal to the tag.We in-troduce an authentication protocol which serves as a proof of concept for authenticating an RFID tag to a reader device using the Advanced Encryption Standard (AES) as cryptographic primitive. Radio frequency identification (RFID) enables you to read data encoded in RFID chips using specialized equipment—RFID readers. Unlike RFID, near-field communication, or NFC, is a two-way channel for transferring data between devices like phones and smartwatches.
RFID key fob readers do more than just user authentication, they play a vital role in access control systems. In addition to authenticating users to gain authorization to enter secure areas, these readers perform other critical functions.
rfid authentication tool
RFID readers can be used throughout an organizational ecosystem for multipurpose authentication with existing employee building-entry ID cards, adding functionality like time-based access control, access to manufacturing processes and hazardous areas. Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and logout authentication, saving time without sacrificing security. To overcome the limitations of the existing schemes and to achieve both security and efficiency together for the IoT, we introduce a novel and efficient RFID authentication protocol-based Elliptic Curve Cryptography (ECC) to maintain security between RFID cards, card readers, and servers.
Learn how HID Global offers RFID technology for secure, efficient and convenient identity verification across various access scenarios. Explore solutions, products, use cases, benefits and resources for RFID authentication.
rfid authentication protocol
Compared to traditional key or password systems, RFID systems enable fast contactless identification, allowing users to simply bring the RFID card close to the reader. The system can also generate real-time entry and exit records for easy management and auditing. RFID reader: This device reads the information stored on the RFID tags and sends it to the access control system to allow authorization. When someone presents their RFID card, ID badge, or key fob to an RFID-enabled door, the reader initiates a signal to the tag.
We in-troduce an authentication protocol which serves as a proof of concept for authenticating an RFID tag to a reader device using the Advanced Encryption Standard (AES) as cryptographic primitive.
Radio frequency identification (RFID) enables you to read data encoded in RFID chips using specialized equipment—RFID readers. Unlike RFID, near-field communication, or NFC, is a two-way channel for transferring data between devices like phones and smartwatches.RFID key fob readers do more than just user authentication, they play a vital role in access control systems. In addition to authenticating users to gain authorization to enter secure areas, these readers perform other critical functions.
RFID readers can be used throughout an organizational ecosystem for multipurpose authentication with existing employee building-entry ID cards, adding functionality like time-based access control, access to manufacturing processes and hazardous areas. Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.Combine RFID credentials with a password for a 2FA solution, or use with other modalities in a full multifactor authentication (MFA) solution. Make passwordless desktop access easy for your users with tap & go login and logout authentication, saving time without sacrificing security.
iso 7816 compliant smart cards
iphone read smart card

rfid authentication algorithm
Wolfpack One Card Office NC State University Box 7307 Raleigh, NC 27695. .
authorization of readers in rfid with password and keys|rfid authentication protocol