smart card authentication flow Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a . ReadID is the first and leading solution for verifying identity documents using smartphones’ NFC. The combination of identity documents with contactless chips and NFC-capable smartphones is the cornerstone of ReadID. ReadID was the .
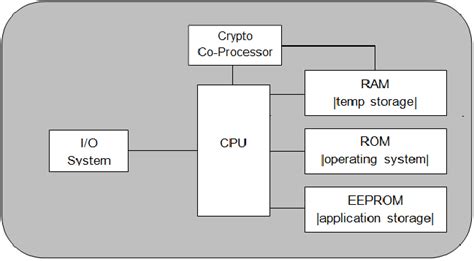
0 · Smart Card Architecture
1 · How does Smart Card Authentication work?
2 · How Smart Card Sign
Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put .
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.The user flow of smart card authentication is as follows. An employee’s identity is tied to company-deployed smart card, which has an embedded chip that is capable of storing and presenting cryptographic keys. Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries.
Smart Card Architecture
Sign in. Ensure that your Smart Card/PIV Card reader is plugged in and your Smart Card/PIV Card is inserted. In a new browser session, go to the Okta sign-in page for your Okta org and click Sign in with PIV / CAC Card.
This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication. Smart cards provide seamless and secure authentication to apps, websites, Wi-Fi, and VPN as well as enable the use of S/MIME to sign and encrypt email. With mobile user productivity becoming commonplace in enterprises, many government and high security customers wonder how to embrace mobility while still maintaining a highly secure environment.
Introduction. These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on .This 101 covers PIV credential basics, including: What PIV is, contains, and looks like. The basics of getting started with PIV credentials. Implementation practices for using PIV for network authentication (smart card logon) are found under implementations. Who is eligible for a .
How does Smart Card Authentication work?
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.The user flow of smart card authentication is as follows. An employee’s identity is tied to company-deployed smart card, which has an embedded chip that is capable of storing and presenting cryptographic keys. Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries.
How Smart Card Sign
Sign in. Ensure that your Smart Card/PIV Card reader is plugged in and your Smart Card/PIV Card is inserted. In a new browser session, go to the Okta sign-in page for your Okta org and click Sign in with PIV / CAC Card.This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication.
Smart cards provide seamless and secure authentication to apps, websites, Wi-Fi, and VPN as well as enable the use of S/MIME to sign and encrypt email. With mobile user productivity becoming commonplace in enterprises, many government and high security customers wonder how to embrace mobility while still maintaining a highly secure environment.Introduction. These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on .

The Hunter Cat NFC is the latest security tool for contactless (Near Field Communication) used in access control, identification and bank cards. Specially created to .
smart card authentication flow|How does Smart Card Authentication work?