how to hack rfid reader Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! NFC playoff picture. Division leaders. Lions: 8-1. Eagles: 7-2. Falcons: 6-4. Cardinals: 6-4. The Eagles are now Detroit’s biggest competitor for the No. 1 seed after a .
0 · What’s On Your Bank Card? Hacker Tool Teaches All About NFC
1 · The ChameleonMini is a skeleton key for RFID
2 · RFID Reader Snoops Cards From 3 Feet Away
3 · RFID Hacking: 6 Common RFID Attacks & 6 Ways to Avoid
4 · Hacking our first MIFAR/RFID Tag
5 · Hacking RFID Tags Is Easier Than You
6 · Hacking MIFARE & RFID
7 · Best RFID Tools for Hacking in 2023
8 · Bambu
9 · Attack Tools – Bishop Fox Resources
10 · #pentestips: How to Bypass a RFID reader without any tools
Actually making them. It’s very simple. Activate NFC on your phone. Make sure .Once your return is received and inspected, we will send you an email to notify you that we have received your returned item. We will also notify you of the approval or rejection of your refund. If you are approved, then your refund will be processed, and a credit will automatically be applied to your credit card or . See more
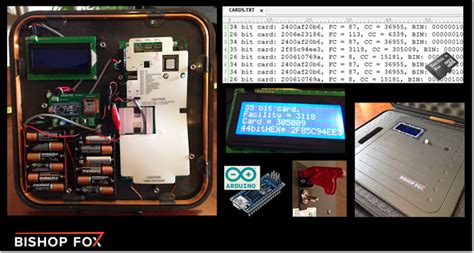
What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, . His solution takes an off-the-shelf high-powered reader, (such as the HID MaxiProx 5375), and makes it amazingly portable by embedding 12 AA batteries and a custom PCB .
The Flipper Zero is a multipurpose hacker tool that aims to make the world of hardware hacking more accessible with a slick design, wide array of capabilities, and a .
driver smart card gemalto
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!BambuLab printers use MiFare 13.56MHZ RFID tags. These tags contain a unique ID that is not encrypted (called the UID) In most cases UID is fixed (not-changable). Some "hackable" rfid . Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak . Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. .
One Time Write RFID tag, the best for duplicating Mifare Classic. In this video you will discover how to bypass an RFID reader by working directly on the door.
What’s On Your Bank Card? Hacker Tool Teaches All About NFC
The easiest and most basic tool to use against MIFARE tags, is MFOC. It tries different keys against a MIFARE tags. What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, but the tricks.

Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas. His solution takes an off-the-shelf high-powered reader, (such as the HID MaxiProx 5375), and makes it amazingly portable by embedding 12 AA batteries and a custom PCB using an Arduino Nano to.
The Flipper Zero is a multipurpose hacker tool that aims to make the world of hardware hacking more accessible with a slick design, wide array of capabilities, and a fantastic looking UI.
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!BambuLab printers use MiFare 13.56MHZ RFID tags. These tags contain a unique ID that is not encrypted (called the UID) In most cases UID is fixed (not-changable). Some "hackable" rfid tags allow you to set the UID to anything you want. Blocks (Encrypted) MiFare tags also contain "Blocks" of data.
Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms.
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers. One Time Write RFID tag, the best for duplicating Mifare Classic. In this video you will discover how to bypass an RFID reader by working directly on the door. The easiest and most basic tool to use against MIFARE tags, is MFOC. It tries different keys against a MIFARE tags.
What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, but the tricks.Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.
debit card smart chip
His solution takes an off-the-shelf high-powered reader, (such as the HID MaxiProx 5375), and makes it amazingly portable by embedding 12 AA batteries and a custom PCB using an Arduino Nano to. The Flipper Zero is a multipurpose hacker tool that aims to make the world of hardware hacking more accessible with a slick design, wide array of capabilities, and a fantastic looking UI. Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!BambuLab printers use MiFare 13.56MHZ RFID tags. These tags contain a unique ID that is not encrypted (called the UID) In most cases UID is fixed (not-changable). Some "hackable" rfid tags allow you to set the UID to anything you want. Blocks (Encrypted) MiFare tags also contain "Blocks" of data.

Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
The ChameleonMini is a skeleton key for RFID
RFID Reader Snoops Cards From 3 Feet Away
One Time Write RFID tag, the best for duplicating Mifare Classic. In this video you will discover how to bypass an RFID reader by working directly on the door.
directv smart card
RFID Hacking: 6 Common RFID Attacks & 6 Ways to Avoid
Visit BBC for trusted reporting on the latest world and US news, sports, business, climate, innovation, culture and much more.
how to hack rfid reader|RFID Hacking: 6 Common RFID Attacks & 6 Ways to Avoid