how to prevent from coping rfid chips integrity By leveraging cryptographic techniques such as digital signatures and message authentication codes, RFID systems can verify the integrity and origin of tag data, thwarting unauthorized access attempts effectively. Auburn Tigers. Get live coverage of SEC college football games with home and away feeds for every team on SiriusXM, including the Auburn Tigers. Hear exclusive interviews with Auburn players and coaches, plus expert analysis .
0 · rfid scanner protection
1 · rfid protection
2 · rfid hacking protection
3 · rfid chip security
4 · rfid chip protection requirements
5 · rfid chip protection definition
6 · how to protect against rfid
7 · how rfid chip is protected
We would like to show you a description here but the site won’t allow us.
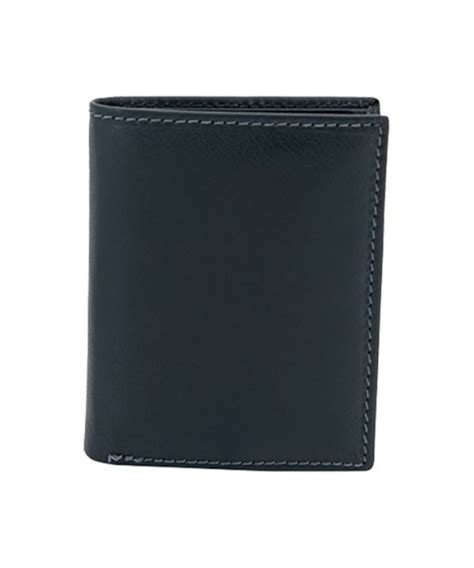
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way to ensure your credentials are .
h mart smart card application
By leveraging cryptographic techniques such as digital signatures and message authentication . One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .By leveraging cryptographic techniques such as digital signatures and message authentication codes, RFID systems can verify the integrity and origin of tag data, thwarting unauthorized access attempts effectively.
The protection of RFID chips is twofold: first, a chip must be protected from unauthorized access (these measures are called Chip Access Control), and ; second, the chip should prevent copying or alteration (these are chip authentication measures).By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from . However, companies are working on security measures to bolster the integrity of RFID, including things like heavy encryption and unique chip identifiers that help prevent interception and cloning. Encrypted tags are way more secure and mostly unhackable.
current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this paper, we discuss four common types of RFID tag attacks .
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
In this article, we’ll discuss how uninvited parties might try to get ahold of your information and eight different ways you can prevent that from happening. First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly.
To prevent counterfeiting casino chips, RFID allows the establishment to program chip detection, making it almost an impossible endeavor to replicate the chips. The key is not simply putting RFID into the chips; it’s programming the whole architecture to be secure against attacks on hardware. Radio-based technology like RFID can be abused by cybercriminals. Seven security suggestions are provided to help you prevent RFID hacking. One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .
By leveraging cryptographic techniques such as digital signatures and message authentication codes, RFID systems can verify the integrity and origin of tag data, thwarting unauthorized access attempts effectively. The protection of RFID chips is twofold: first, a chip must be protected from unauthorized access (these measures are called Chip Access Control), and ; second, the chip should prevent copying or alteration (these are chip authentication measures).
By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from . However, companies are working on security measures to bolster the integrity of RFID, including things like heavy encryption and unique chip identifiers that help prevent interception and cloning. Encrypted tags are way more secure and mostly unhackable.current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this paper, we discuss four common types of RFID tag attacks . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
In this article, we’ll discuss how uninvited parties might try to get ahold of your information and eight different ways you can prevent that from happening. First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly.
To prevent counterfeiting casino chips, RFID allows the establishment to program chip detection, making it almost an impossible endeavor to replicate the chips. The key is not simply putting RFID into the chips; it’s programming the whole architecture to be secure against attacks on hardware.
rfid scanner protection
rfid protection
NFC problem on my iphone 14 pro, the card I used can be read in other iphone 14 .
how to prevent from coping rfid chips integrity|how rfid chip is protected