how to secure rfid tags This publication seeks to assist organizations in understanding the risks of RFID . When it comes to contactless payment cards, there are two types of technology to consider: RFID and NFC. While both technologies allow for contactless transactions, they work in slightly different ways. An RFID card .
0 · what rfid tag will do
1 · rfid tags for home use
2 · rfid radio frequency identification tags
3 · rfid is involved when using
4 · rfid for dummies
5 · rfid cards for beginners
6 · radio frequency identification tags are
7 · example of rfid tags
Once you create a Blinq account, you will need to verify your email add.
This publication seeks to assist organizations in understanding the risks of RFID . Two common methods of this are skimming and eavesdropping: 1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol, it may be at risk of being skimmed. 2.
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.

RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. Radio Frequency Identification (RFID) tags require a radio signal emitted by the receiver in order to read them. Due to this, they operate within a limited distance and are not capable of transmitting large amounts of data. Examples of RFID tags can be seen in credit cards and door passes. Active Tags.
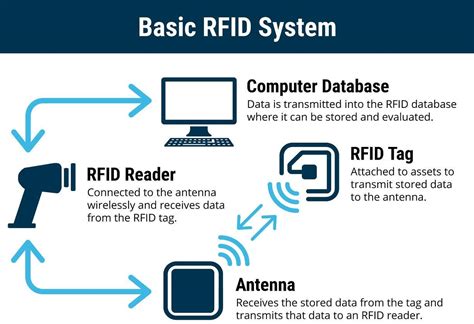
A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
what rfid tag will do
RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider!

Are RFID tags secure? Yes, they can be protected by encryption and authentication protocols, making them more secure than traditional magnetic stripe cards or barcodes. Rec-Products A secure solution is to combine RFID tags with AlpVision’s Fingerprint technology. Fingerprint is a patent technology that leverages the specific characteristics of the product surface to authenticate it.
1. Active RFID tags rely on their own power source to transfer the information to RFID readers. These tags typically have small batteries that need to be replaced periodically. The advantages of active RFID tags are that they offer long communication ranges and continuous tracking. Additionally, they can initiate communication on their own.
Two common methods of this are skimming and eavesdropping: 1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol, it may be at risk of being skimmed. 2.
rfid tags for home use
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. Radio Frequency Identification (RFID) tags require a radio signal emitted by the receiver in order to read them. Due to this, they operate within a limited distance and are not capable of transmitting large amounts of data. Examples of RFID tags can be seen in credit cards and door passes. Active Tags.
A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider!Are RFID tags secure? Yes, they can be protected by encryption and authentication protocols, making them more secure than traditional magnetic stripe cards or barcodes. Rec-Products
A secure solution is to combine RFID tags with AlpVision’s Fingerprint technology. Fingerprint is a patent technology that leverages the specific characteristics of the product surface to authenticate it.
rfid radio frequency identification tags
rf ideas wave id
uhf 4 port rfid readers provider
Sunday, January 4, 2004. 2003 NFC Wild Card Game; Sun 1/4 1 2 3 4 5 F/OT; Seattle (10-6): 3: Pass
how to secure rfid tags|rfid tags for home use