eap authentication security solutions smart cards and biometrics Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily . NFC (Near Field Communication) adalah teknologi komunikasi nirkabel yang memungkinkan perangkat untuk berkomunikasi dengan perangkat lain dalam jarak yang sangat dekat (biasanya kurang dari 10 cm). Cara Kerja. .
0 · windows eap authentication protocol
1 · extensible authentication protocol eap
2 · eap network security
3 · eap method for authentication
4 · eap fast server authentication
5 · eap fast authentication protocol
6 · eap authentication windows 10
7 · eap authentication protocol examples
Using a payment service providerthat enables you to process secure transactions via a wide variety of payment methods will help you to accept payments quickly and easily. With Pay.comyou can easily choose the payment methods you’d like to accept – like . See more
windows eap authentication protocol
where is the rfid chip on a credit card
extensible authentication protocol eap
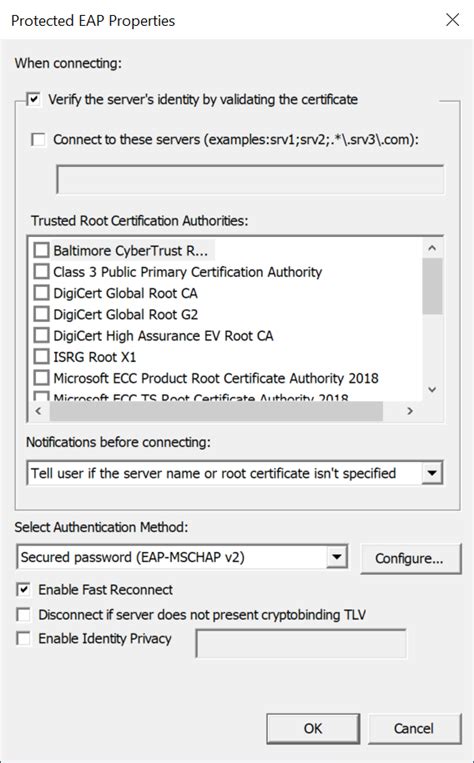
Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily .EAP is used on encrypted networks to provide a secure way to send identifying information to provide network authentication. It supports various authentication methods, including as token .This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .
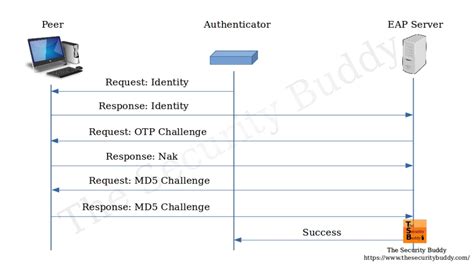
Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily used in network communications.EAP is used on encrypted networks to provide a secure way to send identifying information to provide network authentication. It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption.This flexibility enables EAP to support different authentication mechanisms, such as passwords, digital certificates, smart cards, token-based authentication, biometrics, and more. The EAP framework consists of three main components: the EAP peer, the .
Unlike proximity cards, smart cards using MIFARE DESFire EV1 technology offer several different layers of security, including mutual authentication, which ensures that the reader and the card.EAP is often used in cybersecurity and antivirus solutions to ensure that only authorized users can access sensitive data or systems. EAP enables mutual authentication between the client and server, which ensures that both parties can verify that the other is who they claim to be.
what frequency is my rfid card
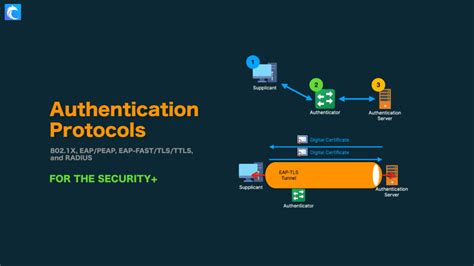
The Extensible Authentication Protocol (EAP) supports a variety of authentication methods, each designed to meet specific security requirements and operational contexts. Among the most significant are EAP-TLS, EAP-TTLS, PEAP, EAP-SIM, and EAP-AKA.The EAP-TLS authentication flow involves a secure exchange of certificates between the user's device and the authentication server, ensuring a trusted connection. Compared to other EAP methods, EAP-TLS provides faster and more secure authentication, making it . An Extensible Authentication Protocol (EAP) is a Local Area Network (LAN) communication and point-to-point (P2P) wireless connecting framework. It helps authenticate clients, computers, or wireless LAN systems to the internet. With Extensible Authentication Protocol, networks can authenticate dial-up connections and LAN networks.EAP-GTC, which stands for Extensible Authentication Protocol Generic Token Card, is a widely used protocol in cybersecurity landscapes to secure systems and protect them against cyber threats and unauthorized access.
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .Extensible Authentication Protocol (EAP) is a flexible framework supporting multiple authentication methods, such as passwords, smart cards, and digital certificates, primarily used in network communications.EAP is used on encrypted networks to provide a secure way to send identifying information to provide network authentication. It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption.
This flexibility enables EAP to support different authentication mechanisms, such as passwords, digital certificates, smart cards, token-based authentication, biometrics, and more. The EAP framework consists of three main components: the EAP peer, the .
Unlike proximity cards, smart cards using MIFARE DESFire EV1 technology offer several different layers of security, including mutual authentication, which ensures that the reader and the card.
EAP is often used in cybersecurity and antivirus solutions to ensure that only authorized users can access sensitive data or systems. EAP enables mutual authentication between the client and server, which ensures that both parties can verify that the other is who they claim to be.
The Extensible Authentication Protocol (EAP) supports a variety of authentication methods, each designed to meet specific security requirements and operational contexts. Among the most significant are EAP-TLS, EAP-TTLS, PEAP, EAP-SIM, and EAP-AKA.
The EAP-TLS authentication flow involves a secure exchange of certificates between the user's device and the authentication server, ensuring a trusted connection. Compared to other EAP methods, EAP-TLS provides faster and more secure authentication, making it . An Extensible Authentication Protocol (EAP) is a Local Area Network (LAN) communication and point-to-point (P2P) wireless connecting framework. It helps authenticate clients, computers, or wireless LAN systems to the internet. With Extensible Authentication Protocol, networks can authenticate dial-up connections and LAN networks.
Send us an email or leave a voicemail and we'll reply within one working day. .
eap authentication security solutions smart cards and biometrics|eap fast authentication protocol