secure symmetric authentication for rfid tags seminar report Starting with a short introduction into common RFID systems with passive tags, we present a . Limitations of passive RFID tags. Despite the many advantages of passive RFID tags, there are still some limitations: Limited reading distance: Depends on the energy activation of the reader, and the reading distance is relatively short. .
0 · Secure symmetric authentication for RFID tags
1 · Secure Symmetric Authentication for RFID Tags
2 · Secure Symmetric Authentication for RFID Tags
Creating the Clone. Take the blank MIFARE Classic card and place it near your phone. In the app, select the write option. In the menu, select the Write Dump (clone) option. Select the dump you got .
In this paper, we demonstrate how the project ART (Authentication for long-range RFID .Starting with a short introduction into common RFID systems with passive tags, we present a .Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. . Targeting RFID tag with short tag ID, we employ a resource friendly symmetric .
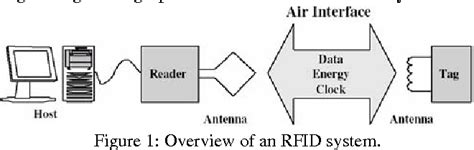
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.
Secure symmetric authentication for RFID tags
Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableIn contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size. Recently, many solutions were proposed to secure RFID systems and many such systems are based on only lightweight primitives, including symmetric encryption, hash functions, and exclusive OR operation.
Strong Authentication for RFID Systems Using the AES Algorithm. Martin Feldhofer Sandra Dominikus J. WolkerstorferIn this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
mifare card price philippines
Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableIn contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.
Recently, many solutions were proposed to secure RFID systems and many such systems are based on only lightweight primitives, including symmetric encryption, hash functions, and exclusive OR operation.
Secure Symmetric Authentication for RFID Tags
mifare card reader writer cloner backup data duplicator software
mifare s50 blank card
The Legend Of Zelda Link (Twilight Princess HD) NFC Card Tag amiibo. $9 49 $9.49. Unit .
secure symmetric authentication for rfid tags seminar report|Secure Symmetric Authentication for RFID Tags