secure symmetric authentication for rfid tags slideshare We present requirements for secure RFID tag ownership transfer, and propose RFID authentication protocols for tag ownership transfer that satisfy these requirements and that have desirable performance characteristics. Visit ESPN for the complete 2024 NFL season Playoff standings. Includes winning percentage, home and away record, and current streak.
0 · SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
1 · Rfid authentication protocols using symmetric cryptography (2)
2 · Presentation On SECURE SYMMETRIC AUTHENTICATION
AFC (1) Dolphins receive a bye (2) Ravens vs. (7) Texans (3) Chiefs vs. (6) Colts (4) Jaguars vs. (5) Browns NFC (1) Eagles receive a bye (2) 49ers vs. (7) Packers (3) Lions vs. (6) Vikings . See more
SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
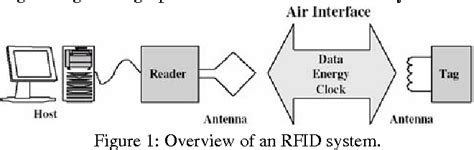
We present requirements for secure RFID tag ownership transfer, and propose .The three main security threats in RFID systems are forgery of tags, unwanted tracking of .
smart card tech
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to . We present requirements for secure RFID tag ownership transfer, and propose RFID authentication protocols for tag ownership transfer that satisfy these requirements and that have desirable performance characteristics.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication. In this paper, we present RBS (Redundant Bit Security) algorithm which is a low-complexity symmetric encryption with a 132-bit secret key. In this algorithm redundant bits are distributed among plaintext data bits to change the location of the plaintext bits in the transmitted data without changing their order.
This secured Gen2 protocol uses a central key stored in the backend database to authenticate tags and provides defense against tracing, skimming, and spoofing attacks through random selection of key segments and use of access passwords.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.Requirements for security-enhanced tag Goals: Prevent forgery (Tag authentication) Prevent unwanted access (Reader auth.) Supply of privacy (Reader authentication) Requirements: Provision of non-predictable nonces Strong cryptographic primitives Standardized symmetric algorithm (AES) Standardized crypto protocol
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how current RFID system is refined to introduce with the project ART (Authentication for long-range RFID systems) by providing secure authentication. Four independent partners, two from industry and two academic partners are implementing this project.Our main contributions in this thesis consist of two proposed RFID authentication schemes. The rst scheme is a symmetric-key-based authentication scheme for low-cost RFID tags. RFID systems used in this scheme conform to EPCglobal Class-1 Generation-2 RFID Speci cation. The work is an improvement of the protocol We present requirements for secure RFID tag ownership transfer, and propose RFID authentication protocols for tag ownership transfer that satisfy these requirements and that have desirable performance characteristics.
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication. In this paper, we present RBS (Redundant Bit Security) algorithm which is a low-complexity symmetric encryption with a 132-bit secret key. In this algorithm redundant bits are distributed among plaintext data bits to change the location of the plaintext bits in the transmitted data without changing their order. This secured Gen2 protocol uses a central key stored in the backend database to authenticate tags and provides defense against tracing, skimming, and spoofing attacks through random selection of key segments and use of access passwords.
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.Requirements for security-enhanced tag Goals: Prevent forgery (Tag authentication) Prevent unwanted access (Reader auth.) Supply of privacy (Reader authentication) Requirements: Provision of non-predictable nonces Strong cryptographic primitives Standardized symmetric algorithm (AES) Standardized crypto protocolThe three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
In this paper, we demonstrate how current RFID system is refined to introduce with the project ART (Authentication for long-range RFID systems) by providing secure authentication. Four independent partners, two from industry and two academic partners are implementing this project.
Rfid authentication protocols using symmetric cryptography (2)
Presentation On SECURE SYMMETRIC AUTHENTICATION
smart card tool windows
.jpg)
Download. 3.0 on 16 votes. The ACR122U NFC Reader is a PC-linked contactless smart card reader/writer developed based on the 13. NFC CSP. Download. NFC Connector is a solution to emulate cryptographic smart card .
secure symmetric authentication for rfid tags slideshare|SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS