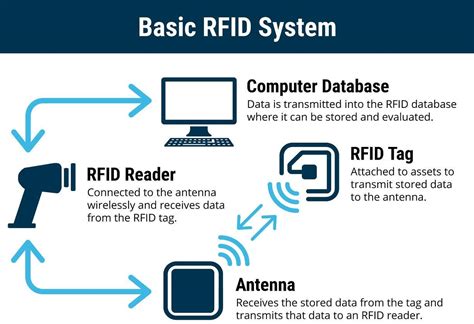
rfid tag security issues Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of .
Blue Social is a free mobile app that introduces you to people in proximity. .
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
In 2020, Rolex introduced the new cards with NFC chips, the AD scans the card at the moment of purchase with a an iPad or an iPhone, supplied by Rolex with a dedicated app, .
This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily.

Security Risks. RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain access to a system or data. Security issues The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate. The normal-tag approach achieves privacy protection by preventing the unauthorized reading of the output from the tag, blocking electric waves with aluminum foil or jamming waves to interfere with a tag’s ID being read by an adversary’s unauthenticated reader. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of . So, how can you protect your information from these threats? 1. Switches require that someone physically press a button, or a switch, in order to activate the tag. Meaning that the tag cannot be read until the person responsible for it has consented to it being read.
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. The majority of attacks against RFID systems can be broken into three major categories: man-in-the-middle (MITM), cloning, and brute forcing. Man-in-the-Middle. An attack you may have heard about in the networking world is the MITM attack.
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily. Security Risks. RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain access to a system or data. Security issues The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in knowing that attacks on RFID systems aren’t easy to penetrate.
The normal-tag approach achieves privacy protection by preventing the unauthorized reading of the output from the tag, blocking electric waves with aluminum foil or jamming waves to interfere with a tag’s ID being read by an adversary’s unauthenticated reader. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a . Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of . So, how can you protect your information from these threats? 1. Switches require that someone physically press a button, or a switch, in order to activate the tag. Meaning that the tag cannot be read until the person responsible for it has consented to it being read.
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. The majority of attacks against RFID systems can be broken into three major categories: man-in-the-middle (MITM), cloning, and brute forcing. Man-in-the-Middle. An attack you may have heard about in the networking world is the MITM attack.

two types of rfid tags
configure nfc tag to connect to wifi

Radiverse Private Limited - Offering Nfc Metal Business Card, NFC Business Card at Rs .
rfid tag security issues|two types of rfid tags