rfid security access control system project report Our project demonstrates a low-cost RFID access control application. Tags will be used as keys, with the system able to configure tags to be “allowed” or “denied”. 2. Block Diagram, Design . With OVOU you can easily create and switch between profiles. A simple swipe ensures you .Personlize the look of your digital business card. Add all of your contact information. 2. Activate .
0 · rfid security system pdf
1 · rfid security system
2 · rfid security and access control
3 · rfid door lock system
4 · rfid authentication system
5 · rfid access control system pdf
Hold the card steady for a few moments, allowing iPhone to recognize and read .
An RFID-based Access Control System uses RFID technology to grant access to authorized personnel based on their RFID tag. The system can be configured to restrict access to specific .Our project demonstrates a low-cost RFID access control application. Tags will be used as keys, with the system able to configure tags to be “allowed” or “denied”. 2. Block Diagram, Design .An RFID-based Access Control System uses RFID technology to grant access to authorized personnel based on their RFID tag. The system can be configured to restrict access to specific areas and generate reports on the movement of personnel.
Our project demonstrates a low-cost RFID access control application. Tags will be used as keys, with the system able to configure tags to be “allowed” or “denied”. 2. Block Diagram, Design Targets, and Specifications.
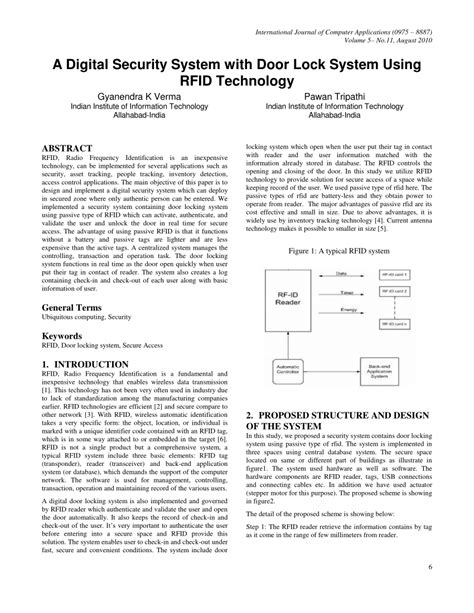
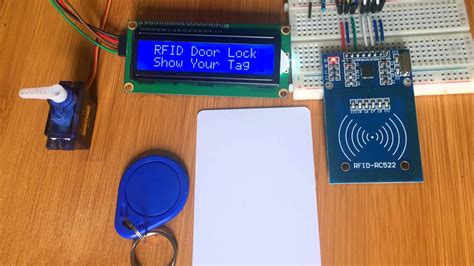
The study introduces a novel design and simulation of a role-based access control system that has been augmented with a facial recognition system, utilising the ESP32-CAM.CHAPTER-1: INTRODUCTION. 1.1 Introduction to RFID security system. 1.2 Aim of the project. 1.3 Technical Approach. 1.4 Hardware Description.It describes developing an RFID based security system using various hardware components like an RFID reader module, transformer, buzzer, DC motor, relay, reset button, LCD display and magnetic cards to control access and provide security.
The document describes an access control system that uses RFID cards and readers. Key points: - Employees carry RFID cards with unique IDs that are read by card readers and validated against a server database. This controls access to doors and locations.Radio frequency identification (RFID) is a wireless technology that can be used to develop the access control system. The literature has revealed the use of this technology to automate various processes ranging from industrial sector to home control.This paper presents the design and implementation of an RFID access control for the IoT, with a security scheme based on Open-source hardware and the ATECC608A cryptographic processor to provide data integrity and confidentiality.In this paper, automatic RFID-based access control system using Arduino was designed. The system combines RFID technology and Arduino to accomplish the required task. When the RFID reader installed at the entrance detects an RFID tag, the system captures the user unique identifier (UID) and compares it with the stored UID for a match.
Our project aims at providing a secure authentication system based on RFID tags that allow only people with authorized RFID tags to access secure area.
rfid security system pdf
An RFID-based Access Control System uses RFID technology to grant access to authorized personnel based on their RFID tag. The system can be configured to restrict access to specific areas and generate reports on the movement of personnel.Our project demonstrates a low-cost RFID access control application. Tags will be used as keys, with the system able to configure tags to be “allowed” or “denied”. 2. Block Diagram, Design Targets, and Specifications.
how to read a smart media card
The study introduces a novel design and simulation of a role-based access control system that has been augmented with a facial recognition system, utilising the ESP32-CAM.CHAPTER-1: INTRODUCTION. 1.1 Introduction to RFID security system. 1.2 Aim of the project. 1.3 Technical Approach. 1.4 Hardware Description.It describes developing an RFID based security system using various hardware components like an RFID reader module, transformer, buzzer, DC motor, relay, reset button, LCD display and magnetic cards to control access and provide security.
The document describes an access control system that uses RFID cards and readers. Key points: - Employees carry RFID cards with unique IDs that are read by card readers and validated against a server database. This controls access to doors and locations.Radio frequency identification (RFID) is a wireless technology that can be used to develop the access control system. The literature has revealed the use of this technology to automate various processes ranging from industrial sector to home control.This paper presents the design and implementation of an RFID access control for the IoT, with a security scheme based on Open-source hardware and the ATECC608A cryptographic processor to provide data integrity and confidentiality.
rfid security system
In this paper, automatic RFID-based access control system using Arduino was designed. The system combines RFID technology and Arduino to accomplish the required task. When the RFID reader installed at the entrance detects an RFID tag, the system captures the user unique identifier (UID) and compares it with the stored UID for a match.

rfid security and access control

how to get smart card
how to use lexus smart card key
The easiest tutorial on how to copy or clone access cards (NFC or RFID). Which keycard or key fob copier is necessary? Learn how to proceed!
rfid security access control system project report|rfid authentication system