smart card security ppt Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, . Get the best deals for nintendo nfc reader nintendo 3ds at eBay.com. We have a great online .
0 · smart card technology ppt
1 · smart card seminar ppt
2 · smart card seminar
3 · smart card security system ppt
4 · seminer smart card
Here are some of my favorite creative ways to use NFC tags with your iPhone. 1. Instantly connect to a Wi-Fi network. One of the biggest pains of living in the digital age is remembering complicated passwords. NFC can .
Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, .The document outlines the history of smart cards from their invention in 1968 to .Smart cards improve security over other machine-readable cards by providing . The document discusses security threats and countermeasures related to smart cards, including physical attacks such as etching the chip surface, side channel attacks like .
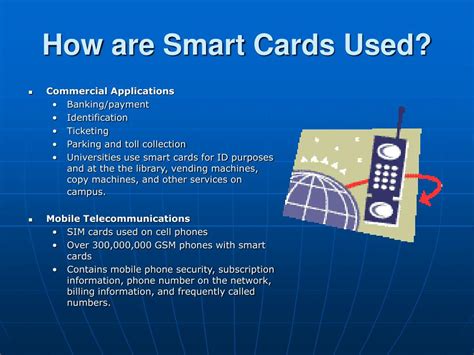
The document outlines the history of smart cards from their invention in 1968 to modern applications. Key benefits include security, portability and ease of use. Examples of smart card applications provided are banking, .
Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, security, portability and increasing storage capacity compared to magnetic stripe cards.
The document discusses security threats and countermeasures related to smart cards, including physical attacks such as etching the chip surface, side channel attacks like power analysis to extract cryptographic keys, and attacks specific to contactless smart cards like covert transactions initiated without user knowledge. The document outlines the history of smart cards from their invention in 1968 to modern applications. Key benefits include security, portability and ease of use. Examples of smart card applications provided are banking, healthcare, access control and telecommunications.
Smart Cards: Technology for Secure Management of Information . Rajat Moona. Computer Science and Engineering. IIT Kanpur. [email protected] Identification 3.1 Smart Cards What Is a Smart Card? Smart cards evolved from plastic identification and magnetic stripe cards through. 1 Hardware - devices for Input. 2 Hardware - devices for Input Processing. Overview • Introduction • Security Technologies • Physical structure and life cycle • Communication with the outside world • Operating system • Attacks on Smart Card • Conclusion. Introduction • Smart card is a credit card sized plastic card embeds an integrated circuit chip.
Title: Smart Cards Created Date: 11/26/2006 4:46:23 PM Document presentation format: On-screen Show Other titles: Times New Roman Arial Wingdings Soaring Smart Cards Overview History of Smart cards PowerPoint Presentation Smart card vs. Magnetic strip card Usage Prime examples Programming the Card Modeling Security Threats Smart Card’s handicap . Smart card security Speaker: 陳 育 麟 Advisor: 陳 中 平 教授. Outline • Introduction of SCAs • Cryptographic Algorithms • Measurements • Hamming Weight • Simple Power Attack (SPA) • Differential Power Attack (DPA) • Countermeasures • My Countermeasure: EPS • Conclusion for EPS. Why Use Smart Card • Security Physical Protection: It is not impossible to open a smart card physically and access data in it. But it is much harder than tampering a workstation. Smart cards improve security over other machine-readable cards by providing secure authentication, encryption, passwords, biometrics and more. Standards like ISO 7816 and 14443 govern smart card interfaces and communication.
Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, security, portability and increasing storage capacity compared to magnetic stripe cards. The document discusses security threats and countermeasures related to smart cards, including physical attacks such as etching the chip surface, side channel attacks like power analysis to extract cryptographic keys, and attacks specific to contactless smart cards like covert transactions initiated without user knowledge.
The document outlines the history of smart cards from their invention in 1968 to modern applications. Key benefits include security, portability and ease of use. Examples of smart card applications provided are banking, healthcare, access control and telecommunications.
Smart Cards: Technology for Secure Management of Information . Rajat Moona. Computer Science and Engineering. IIT Kanpur. [email protected].
Smart Identification 3.1 Smart Cards What Is a Smart Card? Smart cards evolved from plastic identification and magnetic stripe cards through. 1 Hardware - devices for Input. 2 Hardware - devices for Input Processing. Overview • Introduction • Security Technologies • Physical structure and life cycle • Communication with the outside world • Operating system • Attacks on Smart Card • Conclusion. Introduction • Smart card is a credit card sized plastic card embeds an integrated circuit chip.
mini nfc key fob
Title: Smart Cards Created Date: 11/26/2006 4:46:23 PM Document presentation format: On-screen Show Other titles: Times New Roman Arial Wingdings Soaring Smart Cards Overview History of Smart cards PowerPoint Presentation Smart card vs. Magnetic strip card Usage Prime examples Programming the Card Modeling Security Threats Smart Card’s handicap . Smart card security Speaker: 陳 育 麟 Advisor: 陳 中 平 教授. Outline • Introduction of SCAs • Cryptographic Algorithms • Measurements • Hamming Weight • Simple Power Attack (SPA) • Differential Power Attack (DPA) • Countermeasures • My Countermeasure: EPS • Conclusion for EPS.
Why Use Smart Card • Security Physical Protection: It is not impossible to open a smart card physically and access data in it. But it is much harder than tampering a workstation.
smart card technology ppt
nfc key fob loxone
mini nfc key fob iphone
nfc label uitzetten
loxone nfc key fob
NFC tags and readers communicate wirelessly with each other over very .
smart card security ppt|seminer smart card