side channel attacks on smart cards We investigate statistical side channel analysis attacks on the SEED block cipher implemented in two commercial smart cards used in a real-world electronic payment system. .
You can listen to live Auburn Tigers games online or on the radio dial. With 54 stations in the network, the Auburn Sports Network represents one of the biggest and most-listened to college sports network in the South. All home and away .
0 · side channel attacks pdf
1 · cyber security side channels
2 · crypto side channel attacks
NFC Reader. NFCard. NDEF Tools For Android. They are outdated, but still try them. Get them on the default F-Droid. NFCGate is actually for assessing NFC traffic, but it's worth playing .
side channel attacks pdf
nordiac active rfid tags
cyber security side channels
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video.Countermeasures against side channel attacks — e.g. power attacks, based on an analysis of the power consumption, or electromagnetic attacks, which are based on the measurement of . In this paper, the most recent approaches to perform side-channel attacks on smart devices are presented. In addition, we propose defense techniques against this variety of attacks.
In this work, we analyse two well-known classes of physical attacks—fault injections and side-channel attacks—and their application to mobile devices. Such attacks are well . We explore the main forms of attack on smartcards, including ‘side-channel’ attacks which exploit information leaked by the physical characteristics of the card during execution of . We investigate statistical side channel analysis attacks on the SEED block cipher implemented in two commercial smart cards used in a real-world electronic payment system. .

This paper describes an AES Smart Card implementation highly tamper resistant to side channel attacks. Smart Cards are gaining popularity in applications that require high security and store . Vertical side-channel attacks represent a major threat to the confidentiality of enclosed secrets in hardware devices. Fortunately, countermeasures such as blinding or .
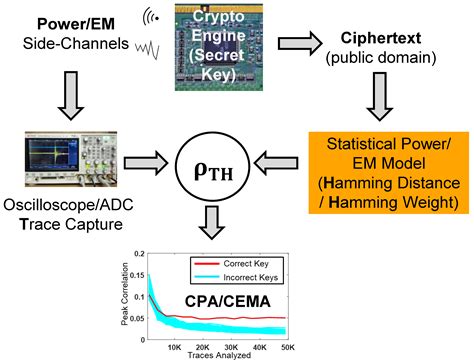
number of people against rfid chip in debit cards
We explore the main forms of attack on smartcards, including 'side-channel' attacks which exploit information leaked by the physical characteristics of the card during execution of . Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video.Countermeasures against side channel attacks — e.g. power attacks, based on an analysis of the power consumption, or electromagnetic attacks, which are based on the measurement of electromagnetic emanation — play an important role in modern implementations of cryptographic algorithms on Smart Cards or other security tokens.Abstract Side-channel attacks are easy-to-implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. These attacks pose a serious threat to .

In this paper, the most recent approaches to perform side-channel attacks on smart devices are presented. In addition, we propose defense techniques against this variety of attacks. In this work, we analyse two well-known classes of physical attacks—fault injections and side-channel attacks—and their application to mobile devices. Such attacks are well-understood in the smart card and secure element (SE) domain (Guilley et al. 2010; Kim and Quisquater 2007; Markantonakis et al. 2009; Quisquater and Samyde 2001). We explore the main forms of attack on smartcards, including ‘side-channel’ attacks which exploit information leaked by the physical characteristics of the card during execution of the algorithm. This extra information can be used to infer secrets.
We investigate statistical side channel analysis attacks on the SEED block cipher implemented in two commercial smart cards used in a real-world electronic payment system. The first one is a contact-only card and the second one is a combination card.
This paper describes an AES Smart Card implementation highly tamper resistant to side channel attacks. Smart Cards are gaining popularity in applications that require high security and store sensitive information.
Vertical side-channel attacks represent a major threat to the confidentiality of enclosed secrets in hardware devices. Fortunately, countermeasures such as blinding or masking are nowadays quasi-systematically used to protect implementations of asymmetric cryptographic algorithms (RSA, ECDSA).
We explore the main forms of attack on smartcards, including 'side-channel' attacks which exploit information leaked by the physical characteristics of the card during execution of the.
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video.Countermeasures against side channel attacks — e.g. power attacks, based on an analysis of the power consumption, or electromagnetic attacks, which are based on the measurement of electromagnetic emanation — play an important role in modern implementations of cryptographic algorithms on Smart Cards or other security tokens.Abstract Side-channel attacks are easy-to-implement whilst powerful attacks against cryptographic implementations, and their targets range from primitives, protocols, modules, and devices to even systems. These attacks pose a serious threat to . In this paper, the most recent approaches to perform side-channel attacks on smart devices are presented. In addition, we propose defense techniques against this variety of attacks.
In this work, we analyse two well-known classes of physical attacks—fault injections and side-channel attacks—and their application to mobile devices. Such attacks are well-understood in the smart card and secure element (SE) domain (Guilley et al. 2010; Kim and Quisquater 2007; Markantonakis et al. 2009; Quisquater and Samyde 2001).
We explore the main forms of attack on smartcards, including ‘side-channel’ attacks which exploit information leaked by the physical characteristics of the card during execution of the algorithm. This extra information can be used to infer secrets. We investigate statistical side channel analysis attacks on the SEED block cipher implemented in two commercial smart cards used in a real-world electronic payment system. The first one is a contact-only card and the second one is a combination card.This paper describes an AES Smart Card implementation highly tamper resistant to side channel attacks. Smart Cards are gaining popularity in applications that require high security and store sensitive information.
Vertical side-channel attacks represent a major threat to the confidentiality of enclosed secrets in hardware devices. Fortunately, countermeasures such as blinding or masking are nowadays quasi-systematically used to protect implementations of asymmetric cryptographic algorithms (RSA, ECDSA).
TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of .
side channel attacks on smart cards|crypto side channel attacks