encrypted rfid reader About this item. 1, Working Frequency: the working frequency of this card duplicator is 125KHz . In Week 18, two games will be played on Saturday (4:30 PM ET and 8:00 PM ET) with the remainder to be played on Sunday afternoon (1:00 PM ET and 4:25 PM ET) and one matchup .
0 · types of rfid readers
1 · rfid readers for sale
2 · rfid reader software windows 10
3 · rfid reader software download
4 · rfid reader meaning
5 · rfid reader function
6 · rfid reader for computer
7 · rfid label reader free online
They are meant to be printed at 300 dpi with dimensions 7.2cm width and 9.7cm height. This gives 0.5cm bleed on all sides that needs to be cut off so that you can have your cards be 6.2 cm by 8.7 cm (Those were the .Botw 23/24/25/26 Cards in 1 Nfc Game Cards Pack for the Legend of Zelda Breath of the Wild .
How would you use symmetric cryptography? The card cannot trust the reader .
About this item. 1, Working Frequency: the working frequency of this card duplicator is 125KHz .
How would you use symmetric cryptography? The card cannot trust the reader (any reader can be used for tampering) and the reader can certainly not trust the card. You could even perform a man-in-the-middle attack with specialist devices.RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or . The remaining methods all rely on some form of encryption, so that the tag and reader can communicate in a way that is indecipherable to outsiders. Since these security measures are encrypted within the tags themselves, they require less effort from the people operating them.
If there’s a need for encryption between the RFID media and the reader, the appropriate credentials are required. There are use cases wherein smart cards or passports store personal information such as name, address, date-of-birth or biometric data. Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.ARC-A is a secure and vandal proof RFID card reader. The most awarded access control reader around the world. An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.
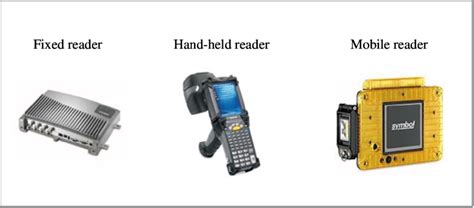
types of rfid readers
To address this, various advanced encryption technologies have been applied to RFID chips to prevent data breaches and unauthorized access. This article will explore these encryption technologies in detail and introduce several well-known .The Mifare Ultralight C uses the Triple Data Encryption Standard (3DES) authentication method to secure communication between the card and the reader. 3DES is a symmetric-key encryption algorithm that uses a 56-bit key to encrypt and decrypt data. The 3DES authentication process involves three steps: Since systems often use the UID as an access measure, hackers can obtain the UID (or keys in the case of broken encryption) by reading existing cards from users and writing that UID to a new card or by simulating it with a device to a reader.
rfid readers for sale
How would you use symmetric cryptography? The card cannot trust the reader (any reader can be used for tampering) and the reader can certainly not trust the card. You could even perform a man-in-the-middle attack with specialist devices.RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or .
The remaining methods all rely on some form of encryption, so that the tag and reader can communicate in a way that is indecipherable to outsiders. Since these security measures are encrypted within the tags themselves, they require less effort from the people operating them. If there’s a need for encryption between the RFID media and the reader, the appropriate credentials are required. There are use cases wherein smart cards or passports store personal information such as name, address, date-of-birth or biometric data.
Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.ARC-A is a secure and vandal proof RFID card reader. The most awarded access control reader around the world. An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.
To address this, various advanced encryption technologies have been applied to RFID chips to prevent data breaches and unauthorized access. This article will explore these encryption technologies in detail and introduce several well-known .The Mifare Ultralight C uses the Triple Data Encryption Standard (3DES) authentication method to secure communication between the card and the reader. 3DES is a symmetric-key encryption algorithm that uses a 56-bit key to encrypt and decrypt data. The 3DES authentication process involves three steps:
rfid uhf logo
rfid reader software windows 10
This aid-filter means that the application will only accept ( 0xA0, 0x00, 0xDA, 0xDA, 0xDA, 0xDA, 0xDA ) AID. But you can change it to any other with length from 5 to 16 or add .
encrypted rfid reader|rfid label reader free online