validating smart card When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an . Load the Amiibo Data: Within the NFC writing app, locate the option to load or import the Amiibo data that you downloaded in Step 1. Select the Amiibo data file and load it into the app. Ready the NFC Tag: Hold the NFC .
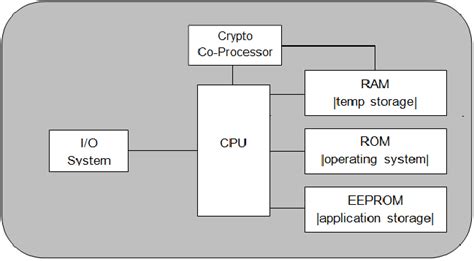
0 · Smart Card Architecture
1 · Conformance testing of the government
I got three of the real ones but I would recommend the same thing which is get a good mix of .
When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an . This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card issues requires a variety of tools and approaches.
When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an imposter. In a networking context, authentication is the act of proving identity to a network application or resource. 1-Restart your computer while holding the SHIFT button. 2-The Advanced Startup menu will open on the boot. 3-Go to Troubleshoot. 4-Now, go to Advanced Options > System restore. 5-Select a restore point and click on next to restore. 6-Then check if . Open services, find smart card. There should be 3 options. If it's a personal pc make sure removal stays disabled but the other two are on automatic. Then open registry edit. Machine. Software. Microsoft. Cryptography. Calais. Then right click smart cards. Permissions. Set everything to full access. And do the same for reader as well. Close .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Follow these easy step-by-step instructions: You will need a computer with a Smart Card reader. Ensure your CAC or PIV is in the computer and select the "Smart Card Login" button on the myPay home page at https://mypay.dfas.mil. . Select the Authentication certificate associated with your CAC or PIV.
When we attempt to logon with a Smart Card we get "The Kerberos Protocol encounterd an error while validating the KDC certificate during Smart Card Logon." In the system log we see the following event: Event ID 9. The certificate is not valid for the requested usage.
How do I know which certificate to select for smart card authentication? Select your current VA or DoD Authentication certificate. Smart card validation is an essential security measure that ensures the authenticity and integrity of smart cards. It plays a critical role in protecting sensitive data and systems from unauthorized access and tampering.
Smart Card Architecture
rfid hospital equipment tracking system
Resolution Option 1. Upgrade the YubiKey Smart Card Minidriver to version 4.1 or higher and it will be able to correctly read certificates from YubiKeys enrolled using the PIV tools. You can download the latest version here. Resolution Option . This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card issues requires a variety of tools and approaches.
When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an imposter. In a networking context, authentication is the act of proving identity to a network application or resource. 1-Restart your computer while holding the SHIFT button. 2-The Advanced Startup menu will open on the boot. 3-Go to Troubleshoot. 4-Now, go to Advanced Options > System restore. 5-Select a restore point and click on next to restore. 6-Then check if . Open services, find smart card. There should be 3 options. If it's a personal pc make sure removal stays disabled but the other two are on automatic. Then open registry edit. Machine. Software. Microsoft. Cryptography. Calais. Then right click smart cards. Permissions. Set everything to full access. And do the same for reader as well. Close .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Follow these easy step-by-step instructions: You will need a computer with a Smart Card reader. Ensure your CAC or PIV is in the computer and select the "Smart Card Login" button on the myPay home page at https://mypay.dfas.mil. . Select the Authentication certificate associated with your CAC or PIV.
rfid based student database management system
When we attempt to logon with a Smart Card we get "The Kerberos Protocol encounterd an error while validating the KDC certificate during Smart Card Logon." In the system log we see the following event: Event ID 9. The certificate is not valid for the requested usage. How do I know which certificate to select for smart card authentication? Select your current VA or DoD Authentication certificate. Smart card validation is an essential security measure that ensures the authenticity and integrity of smart cards. It plays a critical role in protecting sensitive data and systems from unauthorized access and tampering.
Conformance testing of the government
rfid key management systems
Go to NFC -> Detect Reader -> hold flipper to your front door lock. plug your flipper into your .
validating smart card|Smart Card Architecture