explain how smart cards pki maintains data integrity The following three core features make PKI infrastructure an enhanced digital security: Authentication: Identifying a user and a machine in an open environment of the internet is important. PKI ensures that the entities . Late to the party but i use two programs and 1 nfc card. Tagmo to write the amiibo using their .
0 · why pki is important
1 · pki security basics
2 · pki data integrity
3 · pki basics explained
4 · how to use pki
5 · how does pki work
6 · fundamentals of pki
7 · basics of pki 101
Blue Social is a free mobile app that introduces you to people in proximity. .
Protect the integrity of your data (ensure no one secretly modifies data). Cryptographic hashes help you ensure that your data isn’t tampered with in transit. .
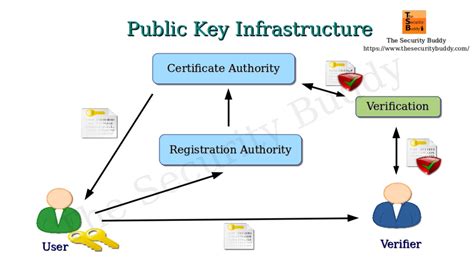
Public key infrastructure (PKI) refers to tools used to create and manage public keys for encryption. Learn what PKI is, how it encrypts communications, and the challenges PKI solves.Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial .It's a system that allows users and machines to securely exchange data over the internet and verify the other party’s identity. For example, when you log in to your online banking account, .
The following three core features make PKI infrastructure an enhanced digital security: Authentication: Identifying a user and a machine in an open environment of the internet is important. PKI ensures that the entities .Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core .At its core, PKI uses asymmetric cryptography to secure confidential information, authenticate users, and validate the integrity and origin of a message. What are the five main components . PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates.
Protect the integrity of your data (ensure no one secretly modifies data). Cryptographic hashes help you ensure that your data isn’t tampered with in transit. Fundamentals of PKI: Asymmetric Cryptography Protects Data on Insecure Networks.Public key infrastructure (PKI) refers to tools used to create and manage public keys for encryption. Learn what PKI is, how it encrypts communications, and the challenges PKI solves.Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial transactions and healthcare records.
It's a system that allows users and machines to securely exchange data over the internet and verify the other party’s identity. For example, when you log in to your online banking account, PKI encrypts the connection and ensures your sensitive information remains private and secure. The following three core features make PKI infrastructure an enhanced digital security: Authentication: Identifying a user and a machine in an open environment of the internet is important. PKI ensures that the entities involved have strong authentication through digital certificates and the verification processes done by CAs.Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core component of data confidentiality, information integrity, authentication, and data access control.At its core, PKI uses asymmetric cryptography to secure confidential information, authenticate users, and validate the integrity and origin of a message. What are the five main components of PKI? 1. Key Pairs: The foundation of Public Key Infrastructure (PKI) is the asymmetric cryptographic key pair, which includes a public key and a private key.
PKI enables a trusted environment by authenticating and ensuring the integrity of data and users. The word “authentication” is of Greek origin, authentikos, meaning “real, genuine.” Authentication is the process of proving something to be true, genuine or valid.
Public key infrastructure (PKI) is a comprehensive framework for assigning, identifying and verifying user identity through digital certificates used for enabling trustworthy and secure digital communications. PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates. Protect the integrity of your data (ensure no one secretly modifies data). Cryptographic hashes help you ensure that your data isn’t tampered with in transit. Fundamentals of PKI: Asymmetric Cryptography Protects Data on Insecure Networks.
why pki is important
Public key infrastructure (PKI) refers to tools used to create and manage public keys for encryption. Learn what PKI is, how it encrypts communications, and the challenges PKI solves.Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial transactions and healthcare records.
It's a system that allows users and machines to securely exchange data over the internet and verify the other party’s identity. For example, when you log in to your online banking account, PKI encrypts the connection and ensures your sensitive information remains private and secure.
The following three core features make PKI infrastructure an enhanced digital security: Authentication: Identifying a user and a machine in an open environment of the internet is important. PKI ensures that the entities involved have strong authentication through digital certificates and the verification processes done by CAs.Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core component of data confidentiality, information integrity, authentication, and data access control.At its core, PKI uses asymmetric cryptography to secure confidential information, authenticate users, and validate the integrity and origin of a message. What are the five main components of PKI? 1. Key Pairs: The foundation of Public Key Infrastructure (PKI) is the asymmetric cryptographic key pair, which includes a public key and a private key.
PKI enables a trusted environment by authenticating and ensuring the integrity of data and users. The word “authentication” is of Greek origin, authentikos, meaning “real, genuine.” Authentication is the process of proving something to be true, genuine or valid.
pki security basics
uhf rfid market size

uhf active rfid noise immunity
pki data integrity
Cashing Out transfers your funds from your Cash App balance to your debit card or bank account. To order yours: Go to the Card tab on your Cash App home screen. Select Get your free card. .
explain how smart cards pki maintains data integrity|basics of pki 101